Knowledge center
Discover our latest news, customer cases and publications.
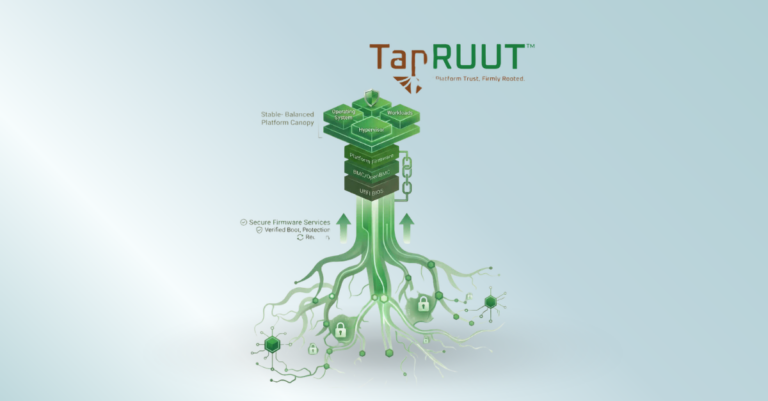
Partner Insyde Software Launches TapRUUT™
Our partner Insyde has launched TapRUUT, a production-ready Platform Root of Trust designed to deliver standards-aligned firmware security across AI PCs, servers and data centers. Built on full NIST SP 800-193 compliance and integrating seamlessly with Insyde's existing UEFI and...
Partner Percepio Brings TraceExporter to VS Code
Percepio's TraceExporter extension brings runtime trace analysis directly into VS Code. Developers can capture and visualize embedded system behavior during debug sessions — without switching tools. Compatible with FreeRTOS, Zephyr, ThreadX and more.
Partner IAR Adds Long Term Support Option
Our partner IAR introduces Long Term Support (LTS) for safety critical development. LTS Services enable teams to maintain stable and reproducible development environments across extended lifecycles. This helps reduce disruption, improve predictability and support compliance in safety critical applications. With...
Embedded World 2026 Recap
Embedded World 2026 once again highlighted the rapid evolution of the embedded industry. From increasing focus on the Cyber Resilience Act (CRA) to the growing adoption of Zephyr OS, the event showcased key trends shaping the future of embedded development....
SEGGER announces new, competitively priced 4-channel Flasher ATE2
Our partner SEGGER has expanded its gang programming portfolio with the Flasher ATE2 (4-channel), a new entry-level single-board in-system programmer. This 4-channel variant is designed to reduce the initial investment for manufacturers while maintaining the high-performance standards of the Flasher...
The revised Product Liability Directive, software is now a product in law
The revised EU Product Liability Directive (PLD) marks a fundamental shift by officially treating software and AI systems as products. This update introduces strict liability for digital goods, meaning consumers can seek compensation for defects without having to prove fault....